Deployment Rule Set
In the beginning, there was just the Deployment Rule Set to try to create white and black lists of Java applets executions. It was basically meant for administrators to block RIAs (Java applets and Java Web Start Applications, known collectively as Rich Internet Applications) by domain, certificates or name. This was great but quite difficult to implement. The steps to get this rule sets,were:
- Create a ruleset in xml. You have to know the syntax… for example:
- Compile it with Java (you would need the JDK).
- Sign it with a trusted certificate of your own. If you do not have one,you have to create it
- Copy it to a standard place in the system.
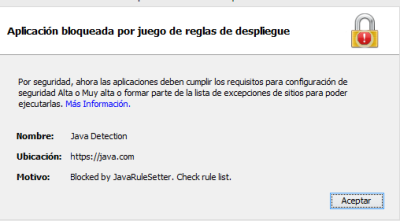
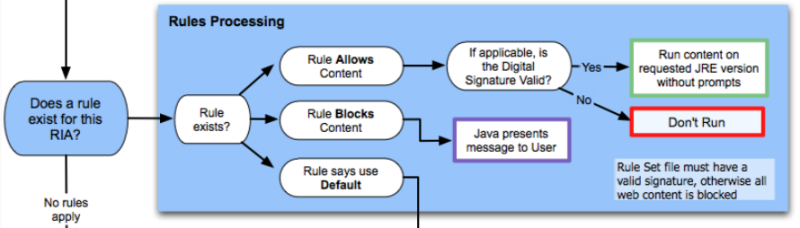
The result was that, when visiting a web page with an applet, this is the decision tree Java follows to run it or not. The rule may block it completely, or allow but only if digitally signed properly. The applet is run without prompts. If set to “default”, it goes to the exception lists decision tree.
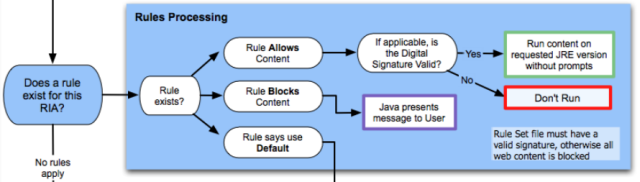 |
| When browser detects a RIA (applet or JWSA) it first goes through this decision system for Deployment Rule Sets |
That was really hard for an administrator and even impossible to achieve for a standard user, so Java reacted creating the Exception Site List. But Rule Sets may very well be used by single users, not only administrators. This is one of the reasons we have just created this tool. To simplify creation of rules for advanced users, and, for creating the whole system for less savvy users (create a certificate, sign it, etc).
Exception Site List
This was created in January 2014 (just months after Deployment rules) for users. It does not require administrative privileges and it is all done via Java interface. It may be seen as a second way to whitelist, but not as powerful as Rule Sets, and as a first layer of defense for a single user.
In a nutshell, Exception Lists affect prompts. It will never make them disappear, but will never make an applet be blocked either, even if security is set to “high”. Exception Lists makes no difference if security level is set to medium. This diagram shows it:
 |
| Exception List flow |
For creating an Exception List, just run javaclp.exe and add a domain. It will work one way or another depending on the Java security configuration.
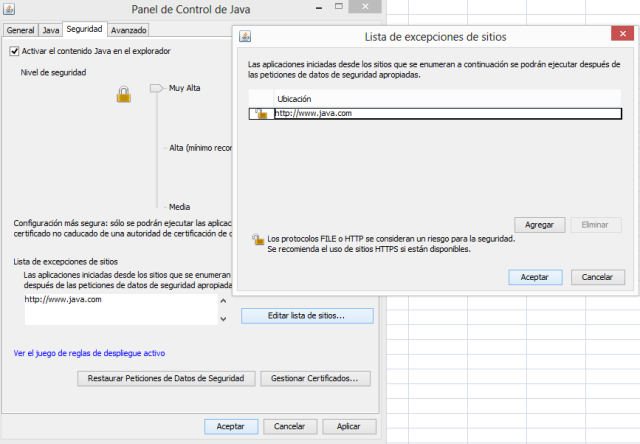 |
| How Exception Lists are configured in Java 7. I may differ a bit in Java 8 |
The file controlling the Exception Site List is stored in the user’s deployment location C:UsersusernameAppDataLocalLowSunJavaDeploymentsecurityexception.sites in Windows.
Rule Sets VS Exception Site Lists
So the main differences are:
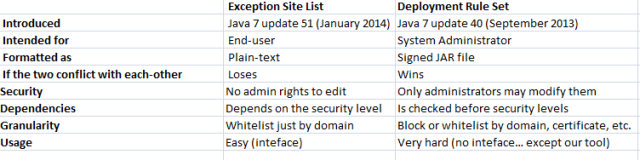 |
| Comparison between Exception Site List and Deployment Rule Set |
Rule Sets allows to create a rule set and distribute to several computers. It wins over Exception Site Lists in case of conflict, and may be modified just by an administrator (not by the user). Another interesting thing is that Rule Sets works on a very early stage. If some day, security levels are defeated, exception site lists would be bypassed, but not the rule sets.
The whole picture
Java is complicated right now. This is the decision flow when executing and applet (or RIA, in general). This is the best way to understand how security has improved in just two years. The complete flow of Java applets executing or not depending on JRE version, Deployment Rules, Exception Lists, etc, is this. Deployment rules work on the second level from start, and Exception lists work on the fifth level.
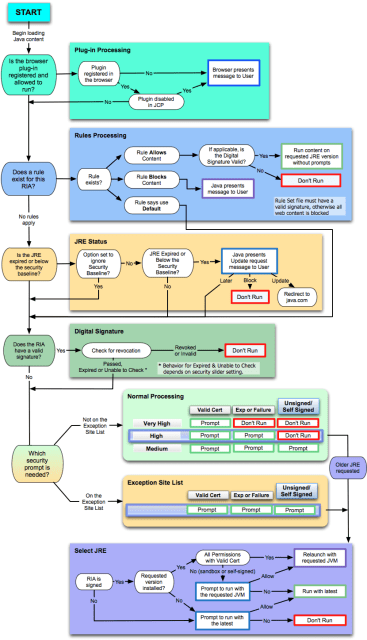 |
| Java, the whole decision picture about RIAs |
The tool
Java Rule Setter is intended for users that are really worried about Java security (they all should) and have to work with it (if you don’t, just uninstall it from the browser).
If you have no idea of what you are doing, just add a domain you need Java to run and click on “Apply changes”. The program will create default settings and apply them.If you are a savvy user, you can use your usual keystore and sign the Deployment Rule file, and skip the whole process. Click on “Advanced mode” for more information.
 |
| Blocking everything will avoid the execution of any applet in a very early stage |
 |
| Browser blocking rules because of the program |
 |
| Adding a new domain to be whitelisted |
 |
| Domain added to be allowed domains |
 |
|
|
There is very basic way to use it. Just run it and add a rule with a domain you want to have in your whitelist (wildcards supported). Click on “Block everything else” and apply changes. You will need to elevate privileges twice: one for adding a cert (only the first time) and one for copying the Rule Set file to system32.
The tool works in GNU/Linux and Mac OS X, although it has not been fully tested in those platforms.
We have created two versions, for Java 8 and Java 7. This tool is in alpha version, so it may contain some bugs. Please report so we can fix them.
To deeply get to know the Deployment Rule Set system and take full advantage of the tool, we recommend reading this official documentation:
http://docs.oracle.com/javase/7/docs/technotes/guides/jweb/security/deployment_rules.html
More information and instructions are available here.






Hi, Great.. Tutorial is just awesome..It is really helpful for a newbie like me.. I am a regular follower of your blog. Really very informative post you shared here. Kindly keep blogging. If anyone wants to become a Java developer learn from Java Training in Chennai. or learn thru Java Online Training in India . Nowadays Java has tons of job opportunities on various vertical industry.