It is, in a way, a similar situation as when we found fake AdBlocks in Google Play and the recent use of Google Play Books as a platform for spreading adware and malware. Chrome Web Store is hosting fake AdBlocks, one of the most popular extensions for browsers. These apps (they are not extensions) are harmless “per se”, since they are just redirectors to some other website where some other programs are offered. Not specially dangerous… by now. This technique may result quite successful for attackers that want to “spam” their content, programs, adware or anything else. Does this mean Chrome Web Store is storing adware/malware directly with these fake apps or extensions? Not at all (they are hosting ad injectors but trying to remove them), but they are allowing developers to upload fake extensions that take advantage of a reputed brand (like AdBlock) to confuse users and get them to download something else. Nothing new, except maybe for the platform used.
How they work
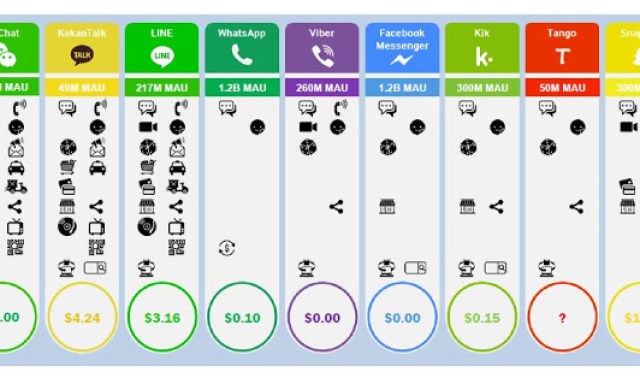
Detected fake AdBlocks are very simple typical Chrome apps. We have found the same program with little differences under several different developer accounts. Here are some samples (not all of them appeared at the same time):
 |
| Some of the AdBlocks detected from different developers |
These apps need no permissions. That is strange and “impossible” if it was a real AdBlock, since these apps should be able at least to read and modify data in the websites you are visiting. Even more, they should be real extensions, rather than apps.
 |
| No permissions needed |
Internally, the only thing these apps do is this:
 |
| Fake AdBlockPlus code (in background.js file) |
- chrome.runtime.onInstalled.addListener: Means that, once the app is installed, this webpage will be opened in Chrome.
- chrome.app.runtime.onLaunched.addListener: Means that, when it is launched, this webpage is opened in Chrome.
URLS to go to are being changed all the time.
Where they go to
These are the links we have seen so far:
- hxxp://www.appforbrowsers.com/adguard.html
- hxxp://www.surprisess.com/adguard.html
- hxxp://www.appforchrome.com/adguard.html
And there are some others that, after going to some kind of app aggregator, redirect to the real AdBlock.
- hxxp://prodownnet.info/adblock-super/
- hxxp://appstoreonline.blogspot.com/search/label/adblock%20chrome
- hxxp://appstoreonline.blogspot.com/search/label/adblock%20youtube
Most of them open websites that encourage the user to download a program called Adguard. A supposed ad-blocker for PC that has its own extensions for different browsers. Is this adware disguised as an anti-adware? Not an easy answer. Google blocks the site if visited with Chrome, at least a few days ago. It means Google (and maybe just them) think or thought some day that this URL should be in a blacklist.
 |
| Google blocking adguard installer a few days ago |
We know that Adguard app was removed (maybe by Google, maybe by the owners) from Google Play last December. Moreover, some engines in VirusTotal, think that this is some kind of malware, detecting it with generic signatures (except Rising, the Chinese AV).
 |
| Some engines detecting the AdGuard installer |
It could be a false positive, something not widely discovered yet, or just this kind of software that are legal and moving on this grey zone where some AV engines have to “respect” them by not detecting them… but are harmful for users once installed anyway.
The only way to know it for sure, would be a manual analysis. A quick analysis shows that the exe itself is changing very often. It is just a downloader for download.adguard.com/setup.exe which is a much more complex program and, again, detected just by one engine with generic signatures… which means nothing. Although Google and some AVs are detecting it, it is, most likely, not a dangerous program. And, probably as well, they are not the ones directly responsible for these fake AdBlocks… They may have a rewarding program for websites bringing downloads… who knows.
Conclusions
The important thing is not fake Chrome Apps pointing to some adware blocker. The conclusions could be:
- Obvious, but any platform is susceptible of being abused and “spammed”. Chrome Web Store is being abused in an “innocent” way (aside the ad injectors) with fake apps, to induce the user to visit and download some other software. Using the same name and icon of reputed programs as a bait, is very effective for attackers… but easy to track and avoid for the store.
- Although it seems to redirect to some software in a “spamming” campaign aimed to get more “visits” and that’s all so far… what if it redirects to some other website? Would it be as effective from the attackers’ standpoint as these ad injectors with 14 million affected users? We may see more apps like this in the future leading to real aggressive adware or malware.
- Users have to be careful interpreting AV results, for good or bad, false positives exist… and of course false negatives do as well. But with enough ratio of both, the average user never really gets to know.







Comuníquese con migo negocios
Buenos días!
Si está interesado en que contactemos con usted, déjenos su comentario y sus datos a través de:
https://www.elevenpaths.com/es/contacta-con-nosotros/index.html
Seguidamente nos pondremos en contacto con usted.
Saludos cordiales del equipo de Eleven Paths.
it works, that is why Google took it off. They make money selling your information and throwing advertisements at you.