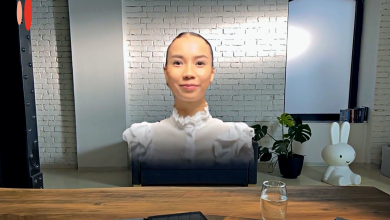
Almudena Bonet Medina
Degree in Audiovisual Communication from the UCM, specializing in Social Listening, Marketing and PR Digital, currently provides a strategic vision in analytical projects focused on the user as Consumer Insights Lead in LUCA Consulting & Analytics. Passionate about the art of telling stories from any discipline and with the data as protagonist.
Popular
Innovation Marketing Team
Innovation Marketing Team
Florence Broderick
Florence Broderick