What is this functionality about?
This new feature implements the TOTP protocol (Time-Based One Time Password), which generates a password valid for a period of time. This password may be requested to users by the services that support it (including the above) as a second factor authentication if the user specified so in the configuration. Thus, users of these services will receive this temporary code in the Latch application installed on their mobile phone, and use it as a second factor authentication (after having been authenticated with their user name and password) to access the services.
What’s new?
Apps already existing in the market for this purpose generate TOTPs associated with the mobile device so that if the user has a problem with it, such as loss or theft, or if they simply have to reset factory data for some reason, they will need to match the services protected with this second factor authentication with the application they use.
In Latch, we have created what we call Cloud TOTP, which consists in, instead of associating the TOTPs with the mobile device, associating them with the Latch account, thus simplifying the recovery process in case of loss of the device.
How can I use it?
To start using this new functionality, you just need to follow these steps:
- First, create a Latch account and install the Latch app on your mobile device.
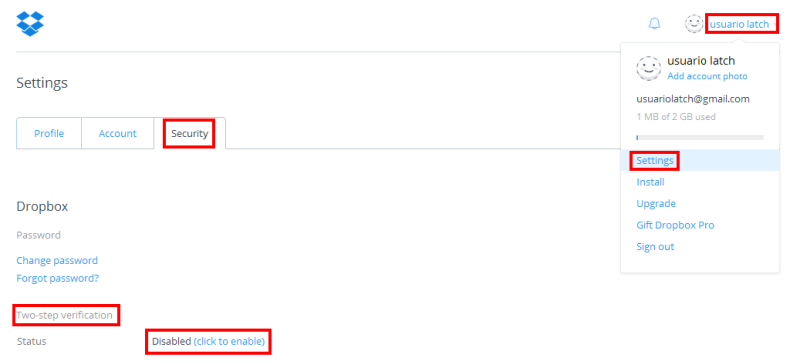
- Then, go to the configuration of the service you want to protect with second factor authentication and enable it. If we take Dropbox as an example, you have to go to the Settings -> Security section, look for the “Two-step verification”, and enable it as shown below, after which you will be guided through a series of screens. When asked how you want to receive security codes, select “Use a mobile app”.
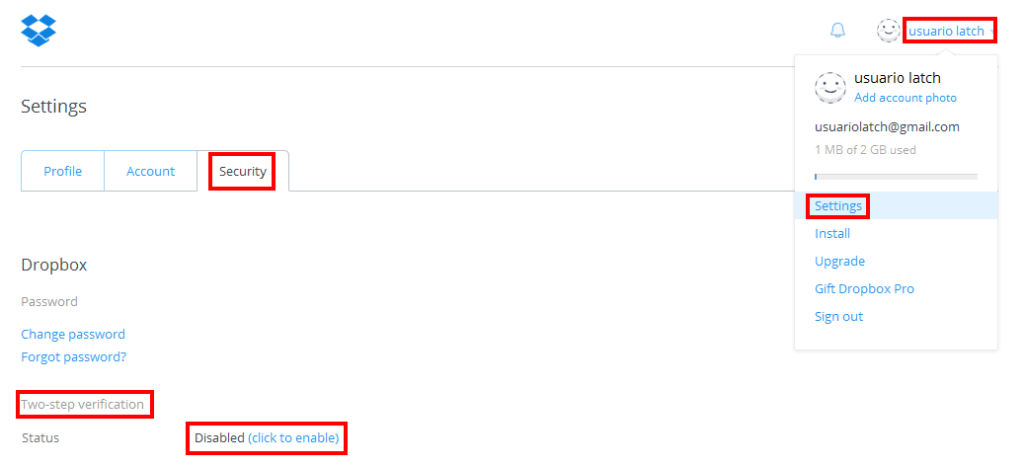 |
| Image 1. Enabling the two-step verification in Dropbox |
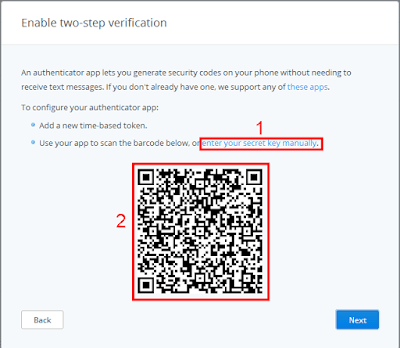 |
| Image 2. Dropbox QR Code |
 |
| Image 3. Capturing the QR code with Latch |
>>Stay tuned! We´ll post video tutorials using Cloud TOTP with services as Dropbox, GitHub, Facebook, Google, etc.






And how to use it with facebook?
We are working on some videos for Facebook and other services like Google, GitHub… Stay tunned to the blog!
el problema es que asocias tu telefono con facebook mediante latch y asocia imei o numero?